We’re excited to announce that Hello Inbox has acquired clearedin.com, a domain name previously owned by a cybersecurity startup that was acquired in 2022.
While we have acquired the domain, it’s important to clarify that this acquisition pertains solely to the domain name and not the company previously associated with it.
This acquisition presents an excellent opportunity for Hello Inbox to expand it’s email deliverability and security tools to businesses worldwide seeking to enhance their email security.
About ClearedIn
ClearedIn focused on cloud collaboration security in the cybersecurity industry.
Its main services included providing anti-phishing protection across various communication and collaboration channels such as chat, email, and file sharing.
It primarily served customers who required compliance and phishing protection, including those using tools like Office 365, Teams, SharePoint Online, and OneDrive.
About Hello Inbox
Hello Inbox provides a free deliverability tester, a comprehensive checklist to fix email deliverability problems and free tools to generate domain authentication records which are important tools in combating email spoofing, phishing, and other email-based threats.
Tools to Enhance Email Deliverability & Security
SPF, DKIM, and DMARC are three email authentication protocols that work together to improve email deliverability and security.
Sender Policy Framework (SPF)
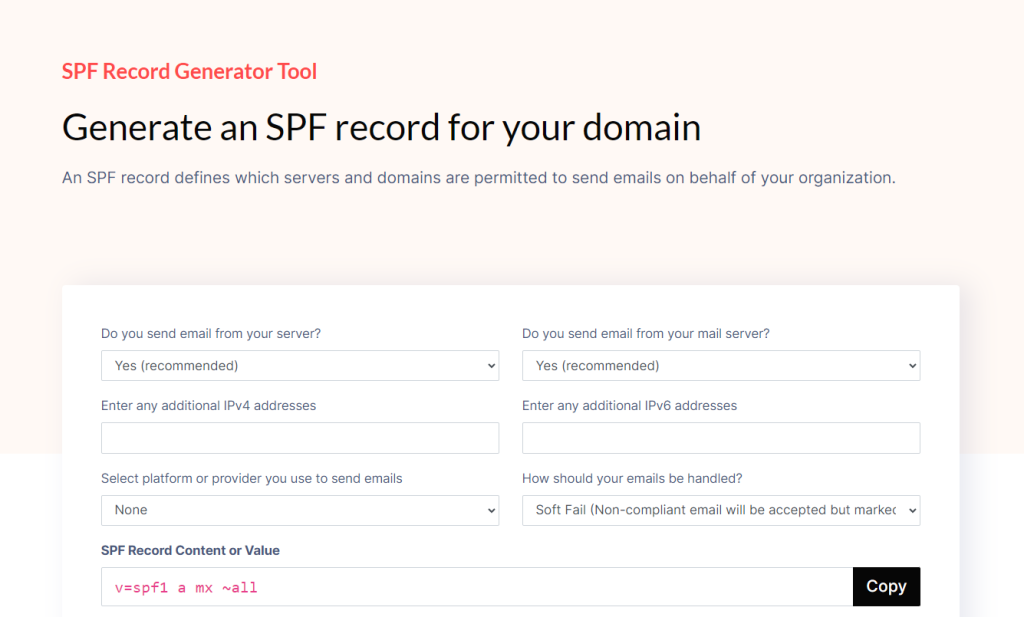
- SPF is a technology that helps to verify the sender’s domain and prevent email spoofing.
- It works by creating a list of authorized sources and IP addresses that are allowed to send emails on behalf of your domain.
- When an email is received, the recipient’s email server can check the SPF record to ensure that the email is coming from a legitimate source.
- This helps to protect your brand from being used in phishing attacks, where cybercriminals might try to impersonate your business to trick recipients into revealing sensitive information or clicking on malicious links.
DomainKeys Identified Mail (DKIM)
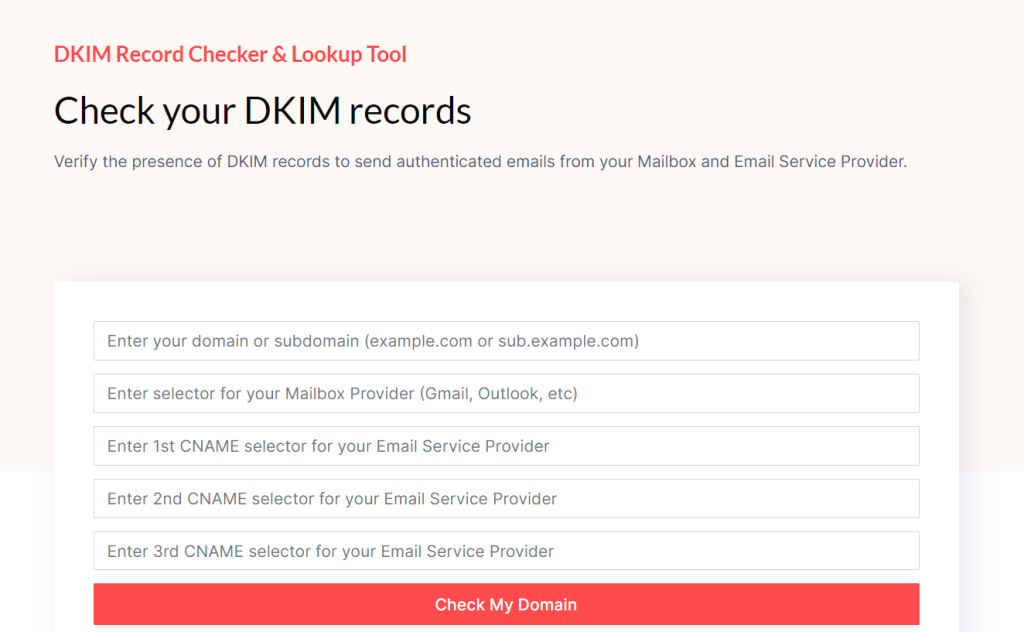
- DKIM is a method of digitally signing emails to verify the authenticity of the sender.
- It adds a digital signature to the email header, which the recipient’s email server can use to verify that the email originated from your domain.
- This helps to prevent email spoofing and ensures that your recipients can trust the emails they receive from your organization.
- DKIM strengthens your brand’s reputation and protects your customers from falling victim to phishing attacks.
Domain-based Message Authentication, Reporting, and Conformance (DMARC)
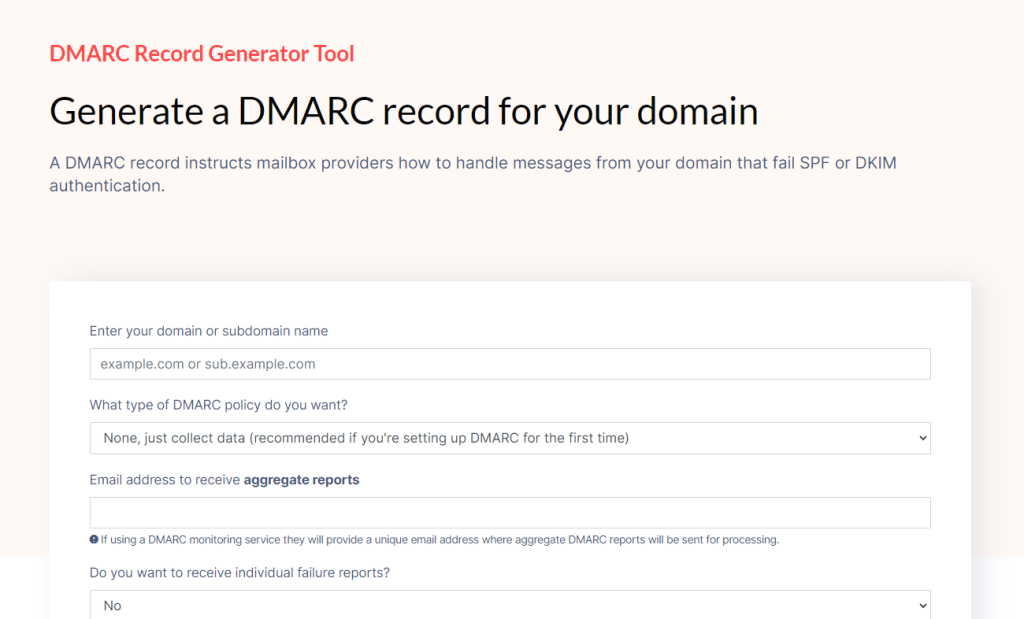
- DMARC builds on the foundations of SPF and DKIM to provide a comprehensive email authentication solution.
- DMARC allows you to specify how your domain should handle emails that fail SPF or DKIM checks.
- It provides reporting capabilities, allowing you to monitor and analyze the email traffic to your domain, including any attempts to spoof your brand.
- DMARC helps to protect your brand by ensuring that only legitimate emails are delivered, and it provides valuable insights into potential security threats.
By implementing these domain authentication protocols, you can greatly reduce the risk of phishing attacks targeting your business and your customers.
It also helps to maintain a strong sender reputation, which is crucial for the successful delivery and inbox placement of your email communications.
Implementing SPF, DKIM, and DMARC demonstrates your commitment to email security and your customers’ trust.
It’s a proactive step towards safeguarding your brand and protecting your recipients from the dangers of email-based threats.
Email security related articles
- Biggest Data Breaches of all Time from Email Phishing
- Reasons Why Spear Phishing Attacks Are Successful
- 10 Eye-Opening Phishing Attack Statistics
- DMARC Compliance Explained
- Typical DMARC Compliance Process: Step-by-Step Guide